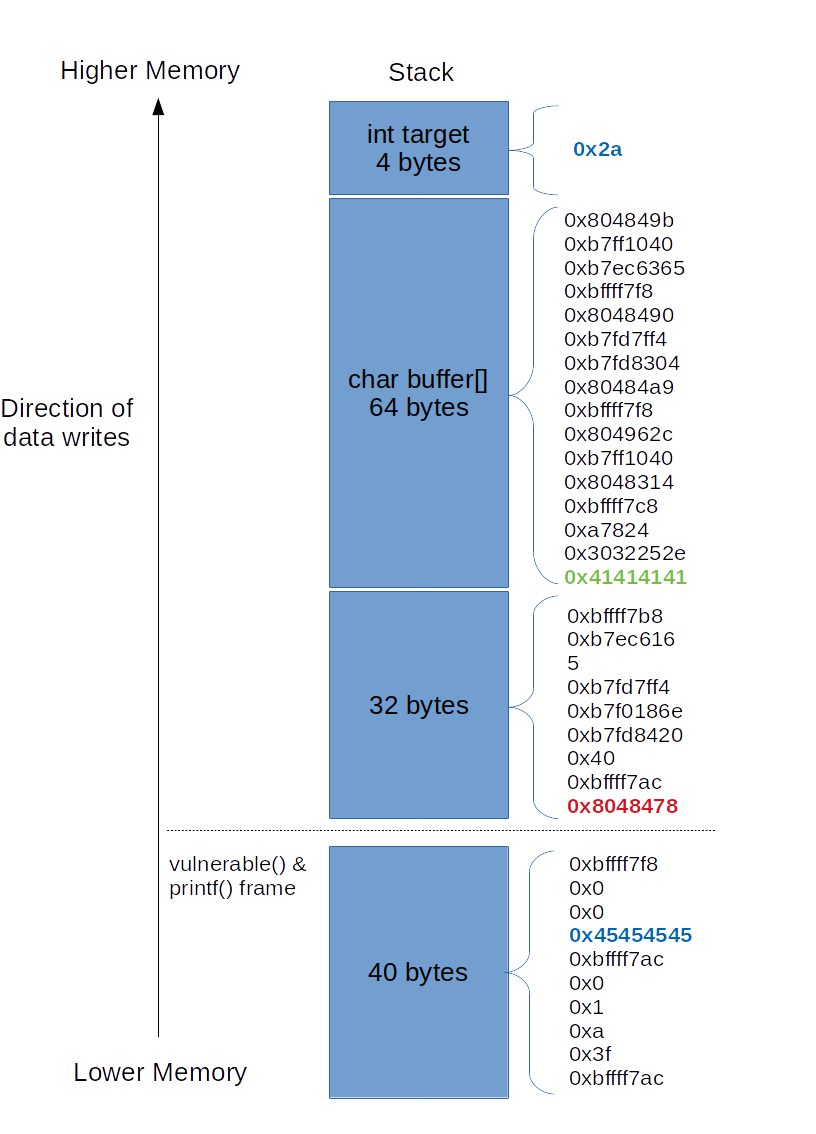
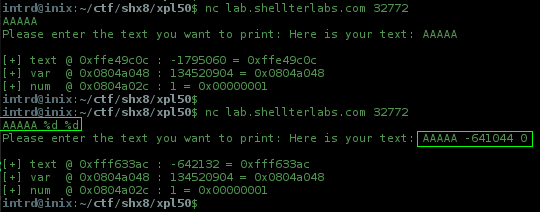
Exploit Development: How to Read & Write to a Program's Memory Using a Format String Vulnerability « Null Byte :: WonderHowTo
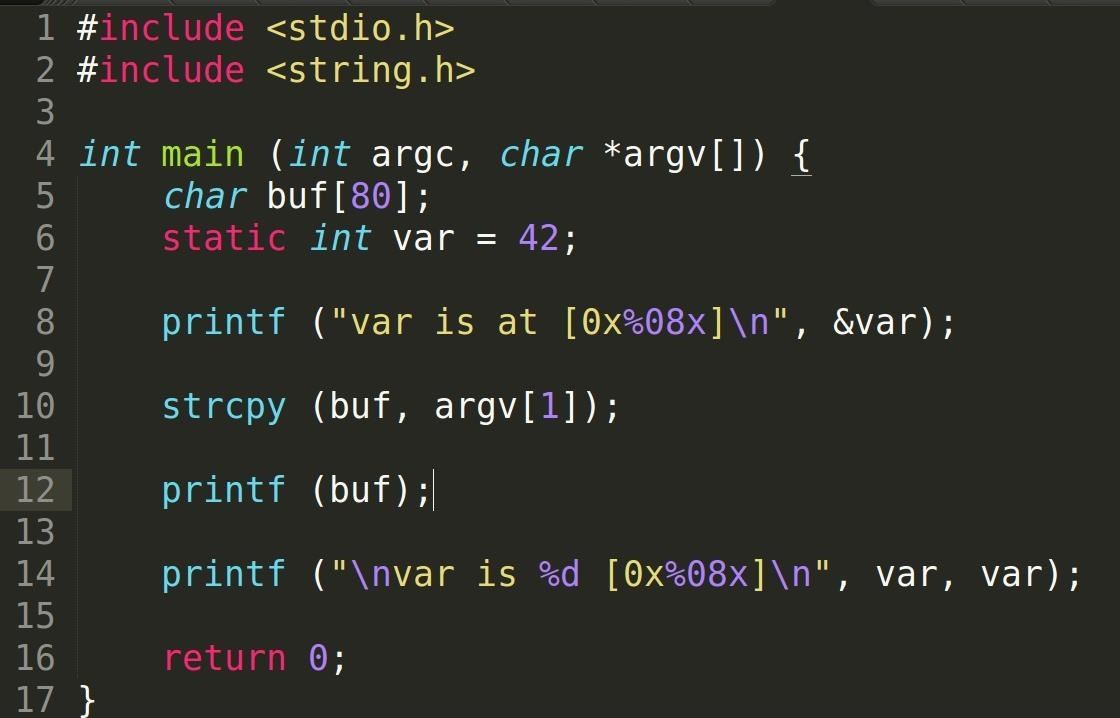
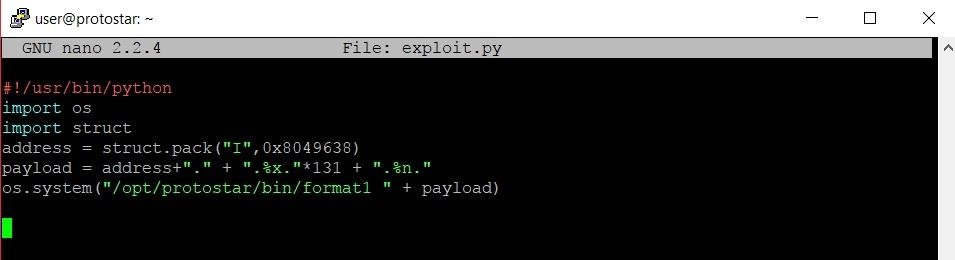
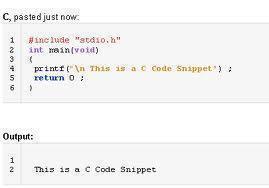
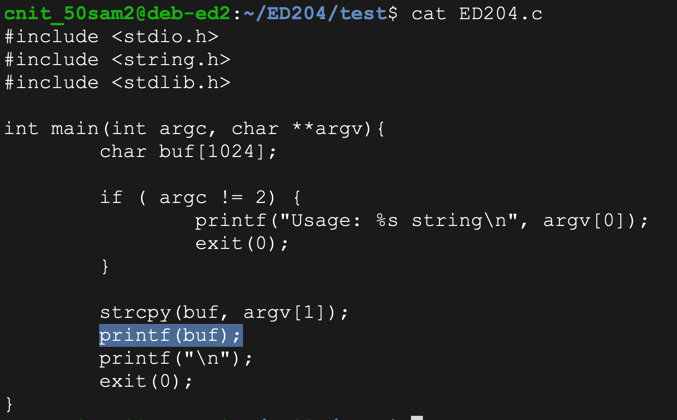
Security-Oriented C Tutorial 0x14 - Format String Vulnerability Part I: Buffer Overflow's Nasty Little Brother « Null Byte :: WonderHowTo

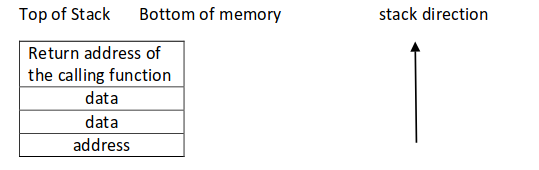
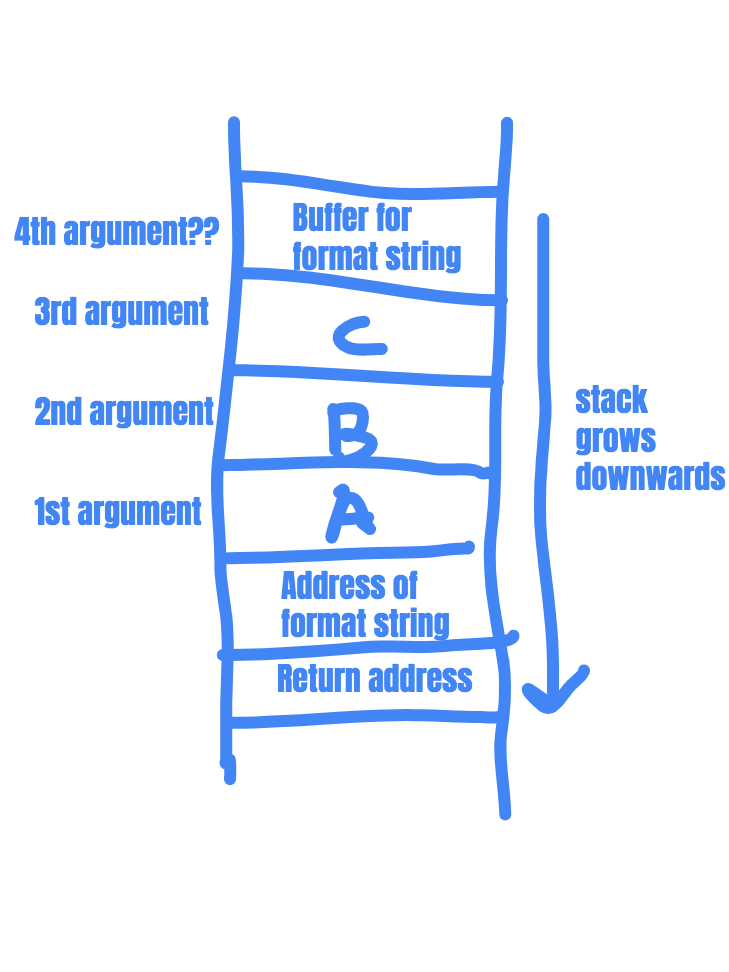
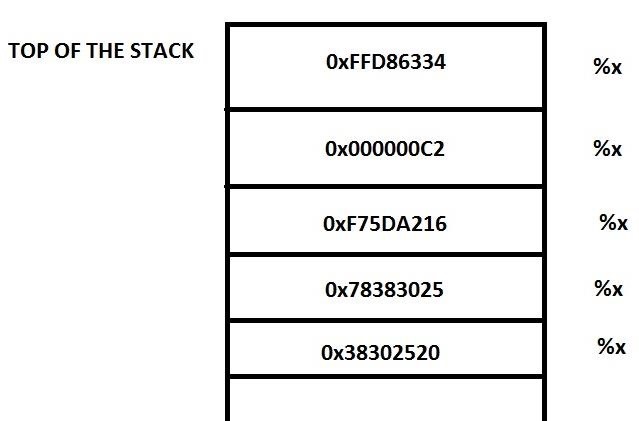
information gathering - Stack behavior on function call during a format string exploit - Information Security Stack Exchange



![Python String Formatting | A Complete Guide For Beginners [ OverView ] Python String Formatting | A Complete Guide For Beginners [ OverView ]](https://www.acte.in/wp-content/uploads/2022/01/String-Interpolation-ACTE.gif)

![Python String Formatting | A Complete Guide For Beginners [ OverView ] Python String Formatting | A Complete Guide For Beginners [ OverView ]](https://www.acte.in/wp-content/uploads/2021/12/Python-String-Formatting-ACTE.jpg)