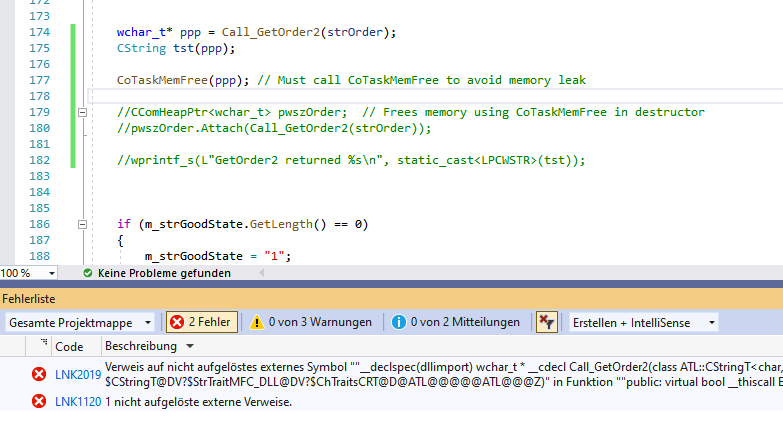
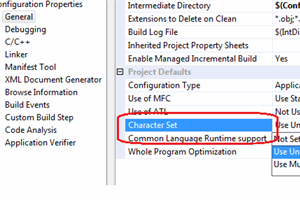
cannot convert 'const char*' to 'LPCWSTR {aka const wchar_t*}' for argument '1' to 'void* FindFirstFileW(LPCWSTR, LPWIN32_FIND_DATAW)' · Issue #1615 · randombit/botan · GitHub
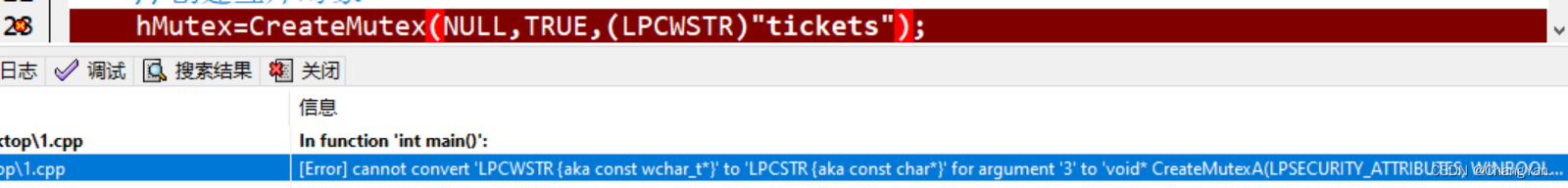
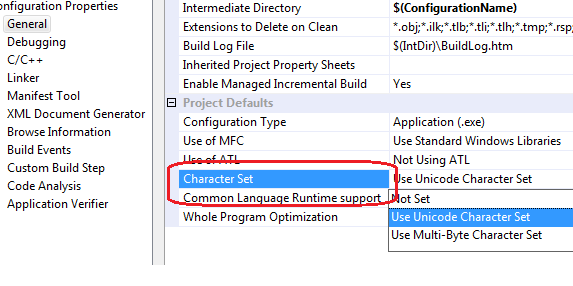
cannot convert 'LPCWSTR {aka const wchar_t*}' to 'LPCSTR {aka const char*}' for argument '3'_cannot convert 'const wchar_t*' to 'lpcstr' {aka '-CSDN博客
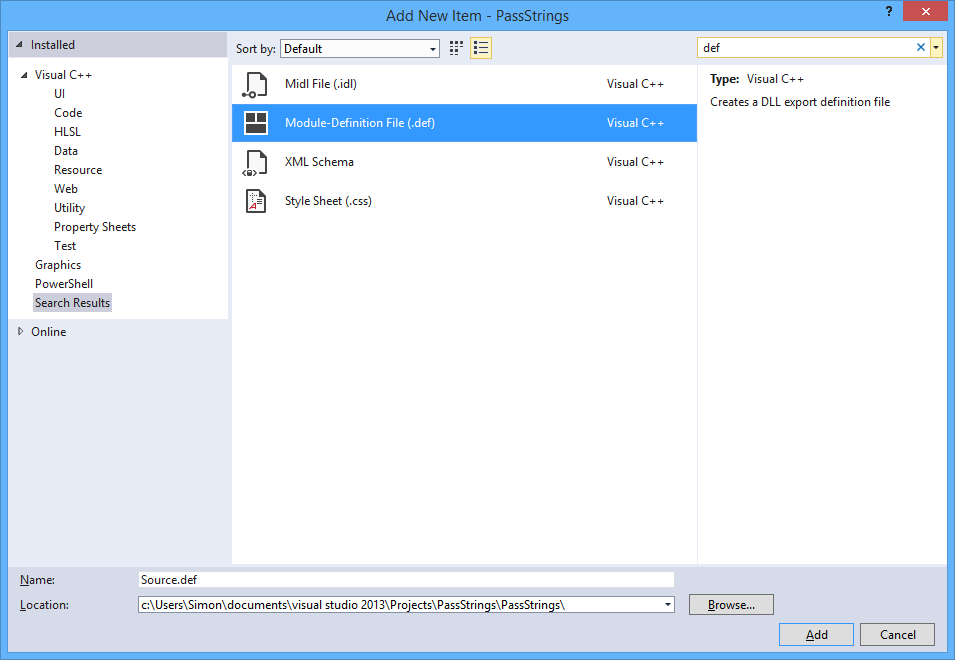
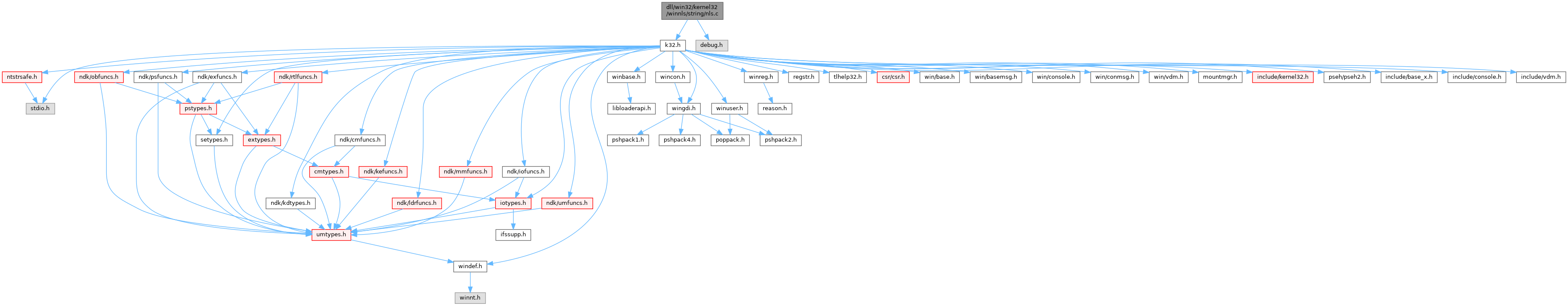
The Excel Development Platform: Easier for a Camel to go through eye of the Needle than to pass strings from VBA to C++ Dll
![Vitali Kremez on Twitter: "3-26-2018: Chinese-suspected cyber espionage tool “#BADFLICK” #backdoor targeting US industries Interesting project🤔: "[Green] pid=%d tid=%d modulePath=%s|" *Loading rev shell and modules via cmd.exe / regsrv32 #DFIR Src ... Vitali Kremez on Twitter: "3-26-2018: Chinese-suspected cyber espionage tool “#BADFLICK” #backdoor targeting US industries Interesting project🤔: "[Green] pid=%d tid=%d modulePath=%s|" *Loading rev shell and modules via cmd.exe / regsrv32 #DFIR Src ...](https://pbs.twimg.com/media/DZQX_vQXcAARz0a.jpg)







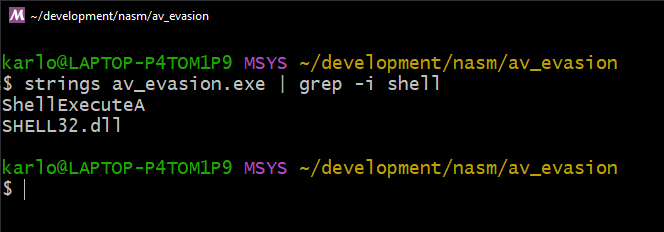
![Information] Introduction to the Windows Subsystem Information] Introduction to the Windows Subsystem](https://i.imgur.com/ub6DwXt.png)